Focus on Compliance or Security?
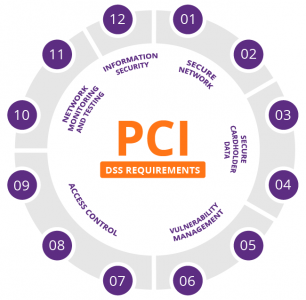
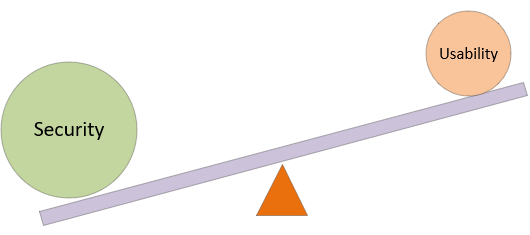
I have posted a few articles about different security standards and frameworks, such as PCI-DSS, The Essential 8, ISO27001, NIST and others – and in my experience, there are some organisations that focus on compliance instead of security. People desperately chase the dogma of maturity levels or complying with every… Continue Reading Focus on Compliance or Security?